Actively targeted by ransomware
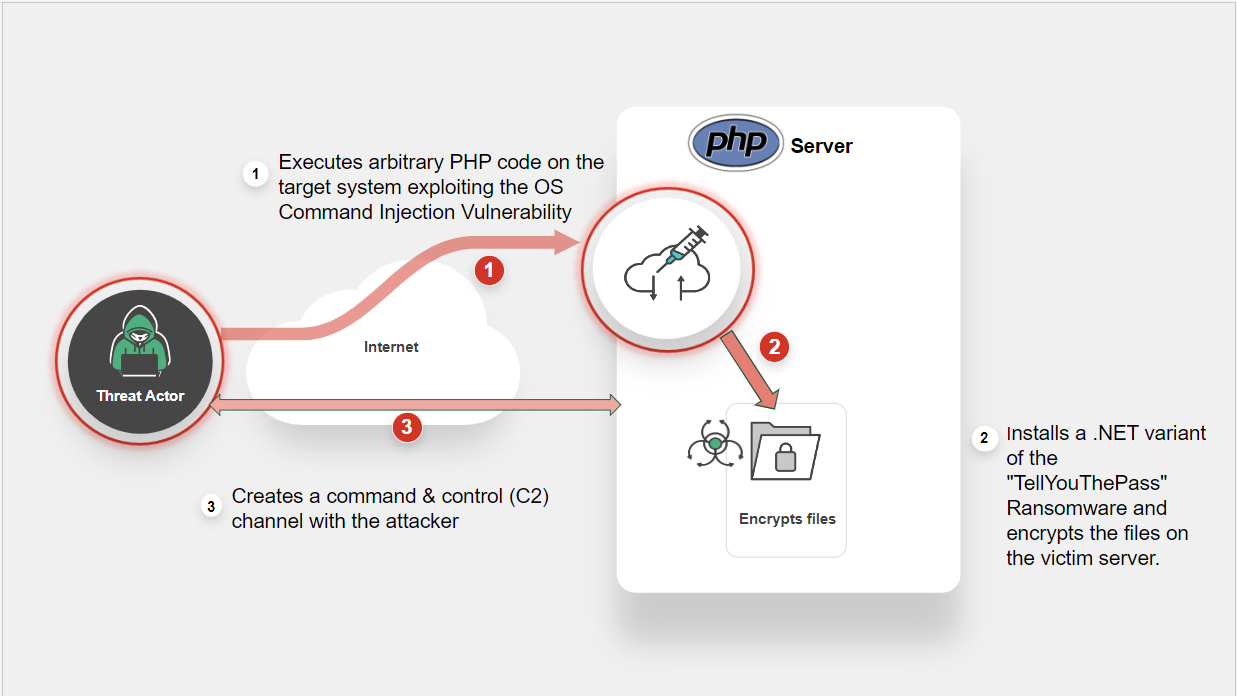
FortiGuard Labs has observed significant level of exploitation attempts targeting the new PHP vulnerability. The TellYouThePass ransomware gang has been leveraging CVE-2024-4577, a remote code execution vulnerability in PHP to deliver web shells and deploy ransomware on targeted systems. Learn More »
Common Vulnerabilities and Exposures
Background
CVE-2024-4577 is an argument injection vulnerability in PHP, specifically Windows-based PHP used in CGI mode, that can be exploited to achieve remote code execution (RCE). This vulnerability is a bypass for the CVE-2012-1823, which is an older vulnerability affecting PHP. Censys has observed about 458,800 instances of potentially vulnerable PHP servers as of June 9, 2024.
TellYouThePass ransomware was previously associated with Log4Shell exploitation, targeting Windows and Linux, and has been active since 2019.
Latest Development
Recent news and incidents related to cybersecurity threats encompassing various events such as data breaches, cyber-attacks, security incidents, and vulnerabilities discovered.
Fortinet customers remain protected through the IPS signature to detect and block the attack attempts targeting the vulnerability. FortiGuard Labs recommends users apply the most recent patch from the vendor to fully mitigate any risks.
-
August 20, 2024: A newly discovered backdoor, dubbed Msupedge, was used in an attack exploiting the PHP vulnerability (CVE-2024-4577).
https://symantec-enterprise-blogs.security.com/threat-intelligence/taiwan-malware-dns -
July 11, 2024: Multiple malware campaigns targets the PHP vulnerability: Gh0st RAT, RedTail crypto miners, and XMRig.
https://www.akamai.com/blog/security-research/2024-php-exploit-cve-one-day-after-disclosure#rat -
June 12, 2024: FortiGuard telemetery shows attack attempts targeting 40,000+ unique IPS devices
-
June 12, 2024: CISA released a Cybersecurity Advisory on Threat Actors Exploiting Vulnerabilities in Ivanti Connect Secure and Policy Secure Gateways
https://www.cisa.gov/known-exploited-vulnerabilities-catalog -
June 10, 2024: Imperva Threat Research reported on attacker activity leveraging the new PHP vulnerability.
https://www.imperva.com/blog/update-cve-2024-4577-quickly-weaponized-to-distribute-tellyouthepass-ransomware/ -
June 07, 2024: Researchers at watchTowr released a proof-of-concept (PoC) script for CVE-2024-4577 on their GitHub page.
https://github.com/watchtowrlabs/CVE-2024-4577 -
June 06, 2024: Patched versions were released by PHP to address this vulnerability.
https://www.php.net/
FortiGuard Cybersecurity Framework
Mitigate security threats and vulnerabilities by leveraging the range of FortiGuard Services.
-
Lure
-
Decoy VM
-
AV
-
Vulnerability
-
AV (Pre-filter)
-
Behavior Detection
-
IPS
-
Web App Security
-
Post-execution
-
IOC
-
Outbreak Detection
-
Threat Hunting
-
Content Update
-
Playbook
-
Automated Response
-
Assisted Response Services
-
NOC/SOC Training
-
End-User Training
-
Vulnerability Management
-
Attack Surface Hardening
-
Business Reputation
-
Attack Surface Monitoring (Inside & Outside)
Threat Intelligence
Information gathered from analyzing ongoing cybersecurity events including threat actors, their tactics, techniques, and procedures (TTPs), indicators of compromise (IOCs), malware and related vulnerabilities.
References
Sources of information in support and relation to this Outbreak and vendor.