An actively exploited critical vulnerability in the PAN-OS Global Protect
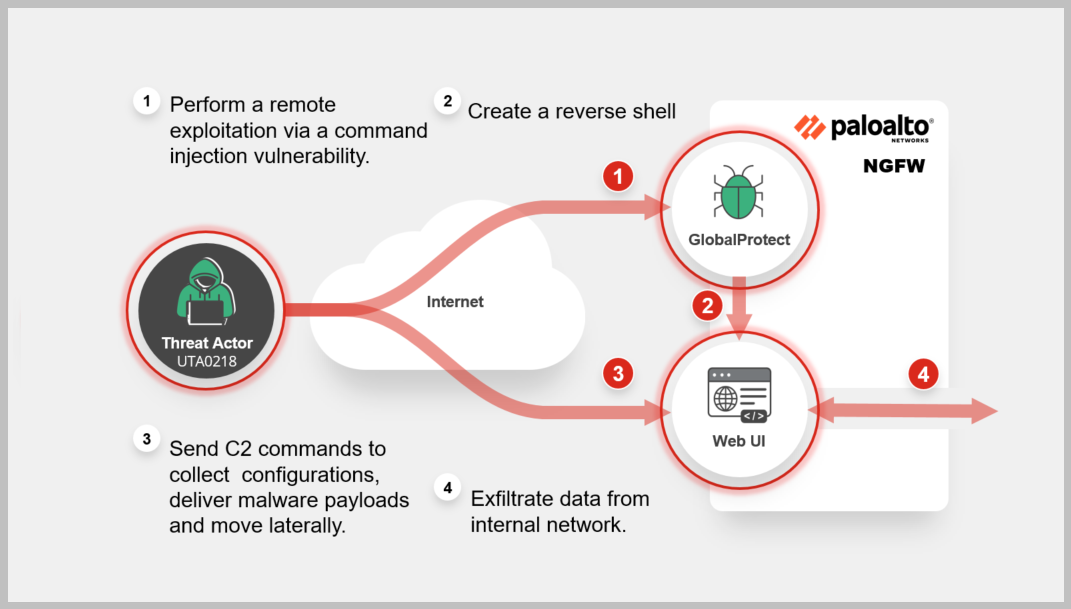
The attack on PAN-OS GlobalProtect devices identified as CVE-2024-3400 allows a malicious actor to remotely exploit an unauthenticated command injection vulnerability that leads to remote code execution. Once established, the attacker can further collect configurations, deliver malware payloads and move laterally into the network. Learn More »
Common Vulnerabilities and Exposures
Background
The GlobalProtect Gateway provides security solution for roaming users by extending the same next-generation firewall-based policies.
Latest Development
Recent news and incidents related to cybersecurity threats encompassing various events such as data breaches, cyber-attacks, security incidents, and vulnerabilities discovered.
The FortiGuard is continuously monitoring and investigating the attack to increase protection coverages and reduce the attack surface.
-
September 25, 2025: RedNovember (which overlaps with Storm-2077) targeted perimeter appliances of high-profile organizations globally.
https://www.recordedfuture.com/research/rednovember-targets-government-defense-and-technology-organizations -
September 02, 2025: People's Republic of China (PRC) state-sponsored cyber threat actors are targeting networks globally.
https://www.cisa.gov/news-events/cybersecurity-advisories/aa25-239a?utm_source=SaltTyphoon&utm_medium=GovDelivery -
March 05, 2025: In March 2024, Silk Typhoon used a zero-day exploit for CVE-2024-3400 in GlobalProtect Gateway on Palo Alto Networks firewalls to compromise multiple organizations.
https://www.microsoft.com/en-us/security/blog/2025/03/05/silk-typhoon-targeting-it-supply-chain/ -
April 15, 2024: FortiGuard released an IPS signature to detect and block exploitation attempts targetting edge devices. Also, FortiGuard published an Outbreak walkthrough video.
https://www.fortiguard.com/encyclopedia/ips/55555 -
April 12, 2024: FortiGuard published this Outbreak Alert report.
-
April 12, 2024: FortiGuard issued a Threat Signal.
https://www.fortiguard.com/threat-signal-report/5423/pan-os-critical-flaw-in-globalprotect-gateway-cve-2024-3400 -
April 11, 2024: Palo Alto Networks released a security advisory on their GlobalProtect.
https://security.paloaltonetworks.com/CVE-2024-3400 -
April 10, 2024: Volexity identified zero-day exploitation of a vulnerability found within the GlobalProtect.
https://www.volexity.com/blog/2024/04/12/zero-day-exploitation-of-unauthenticated-remote-code-execution-vulnerability-in-globalprotect-cve-2024-3400/
FortiGuard Cybersecurity Framework
Mitigate security threats and vulnerabilities by leveraging the range of FortiGuard Services.
-
Lure
-
Decoy VM
-
AV
-
IPS
-
Web App Security
-
IOC
-
Outbreak Detection
-
Threat Hunting
-
Playbook
-
Automated Response
-
Assisted Response Services
-
NOC/SOC Training
-
End-User Training
-
Attack Surface Hardening
-
Business Reputation
-
Attack Surface Monitoring (Inside & Outside)
-
Inventory Management
Threat Intelligence
Information gathered from analyzing ongoing cybersecurity events including threat actors, their tactics, techniques, and procedures (TTPs), indicators of compromise (IOCs), malware and related vulnerabilities.
References
Sources of information in support and relation to this Outbreak and vendor.