NetScaler ADC and NetScaler Gateway Vulnerability Actively Exploited
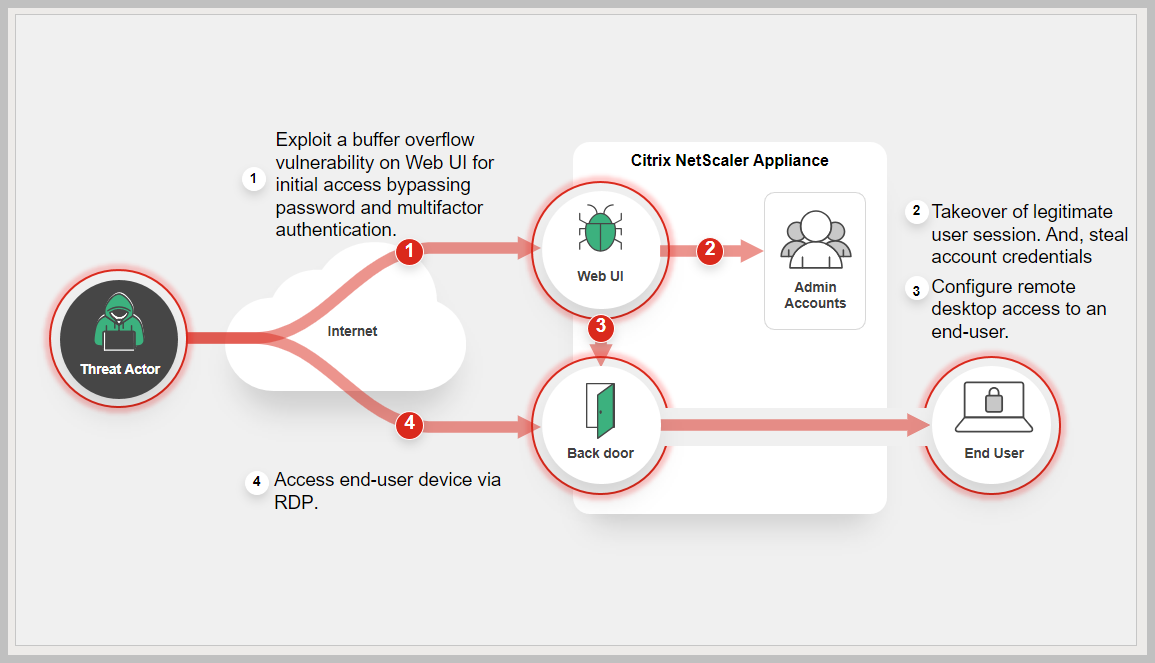
CVE-2023-4966 is being widely exploited, with multiple threat actors, including ransomware groups, targeting internet-accessible NetScaler ADC and Gateway instances. After exploiting CVE-2023-4966, the attackers may engage in network reconnaissance, stealing account credentials and moving laterally via RDP. Learn More »
Common Vulnerabilities and Exposures
Background
Citrix Netscaler is a network device providing load balancing, firewall and VPN services. NetScaler Gateway usually refers to the VPN and authentication components, whereas ADC refers to the load balancing and traffic management features. CVE-2023-4966 is a sensitive information disclosure vulnerability in NetScaler ADC and NetScaler Gateway .
As of October 30, Shadowserver spotted just over 5,000 vulnerable servers on the public internet.
Latest Development
Recent news and incidents related to cybersecurity threats encompassing various events such as data breaches, cyber-attacks, security incidents, and vulnerabilities discovered.
Oct. 10, 2023: Citrix released a security bulletin for a sensitive information disclosure vulnerability (CVE-2023-4966) impacting NetScaler ADC and NetScaler Gateway appliances. https://support.citrix.com/article/CTX579459/
Oct 18, 2023: CISA added CVE-2023-4966 to its known exploited list, KEV catalog.
Oct 25, 2023 AssetNote researchers released a proof-of-concept (PoC) exploit demonstrating how to hijack a NetScaler account via session token theft.
Oct 31, 2023: Mandiant released campaign analysis targeting CVE-2023-4966
https://www.mandiant.com/resources/blog/session-hijacking-citrix-cve-2023-4966
Fortinet customers remain protected via the IPS signature "HTTP.Header.Overly.Long.Host.Field.Value" to detect and block any attack targeting the vulnerable Citrix servers and as of now, it has blocked attacks targeting the vulnerability on more than 5000 unique IPS devices.
FortiGuard also recommends to update and apply patches provided on the vendor advisory.
https://www.netscaler.com/blog/news/cve-2023-4966-critical-security-update-now-available-for-netscaler-adc-and-netscaler-gateway/
FortiGuard Cybersecurity Framework
Mitigate security threats and vulnerabilities by leveraging the range of FortiGuard Services.
-
IPS
-
Outbreak Detection
-
Threat Hunting
-
Assisted Response Services
-
Automated Response
-
NOC/SOC Training
-
End-User Training
-
Attack Surface Hardening
-
Business Reputation
Threat Intelligence
Information gathered from analyzing ongoing cybersecurity events including threat actors, their tactics, techniques, and procedures (TTPs), indicators of compromise (IOCs), malware and related vulnerabilities.
References
Sources of information in support and relation to this Outbreak and vendor.