Critical-level detections in the wild
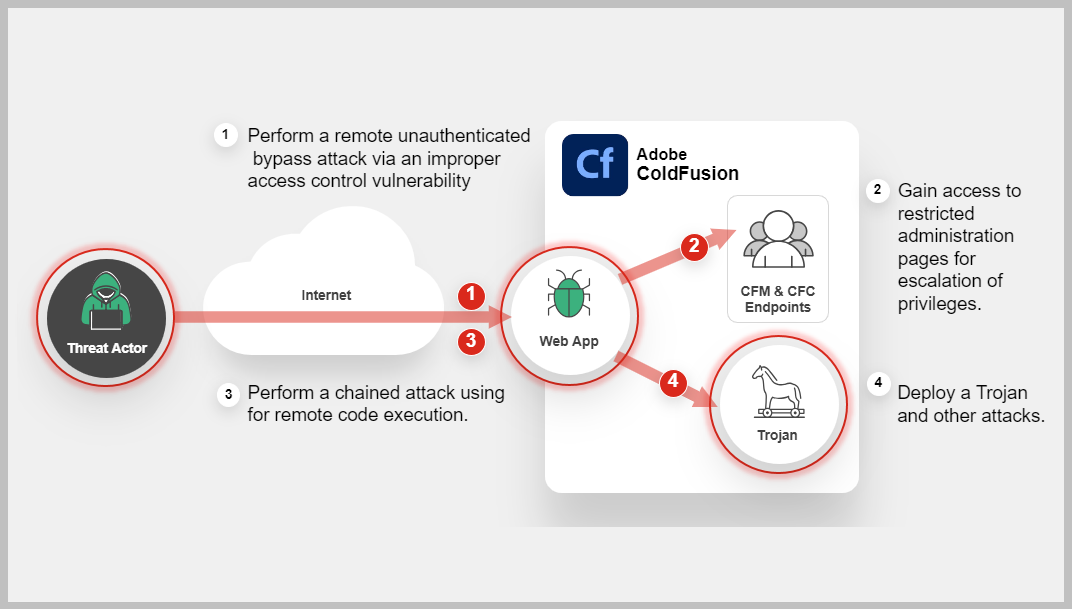
FortiGuards labs observed extremely widespread exploitation attempts relating to security bypass vulnerabilities in Adobe ColdFusion. Successful exploitation could result in access of the ColdFusion Administrator endpoints. Learn More »
Common Vulnerabilities and Exposures
Background
Adobe ColdFusion is a commercial rapid web-application development computing platform to rapidly build, test and deploy web applications. Previously, in Aug 2023, we saw it being actively targeted by the attackers to exploit CVE-2023-26359, CVE-2023-26360 which lead to the release of an Outbreak Alert at that time, to read the full Outbreak visit: https://www.fortiguard.com/outbreak-alert/adobe-coldfusion-code-execution
Latest Development
Recent news and incidents related to cybersecurity threats encompassing various events such as data breaches, cyber-attacks, security incidents, and vulnerabilities discovered.
-
January 09, 2024: FortiGuard Labs observed critical level of continued attacks on Adobe Coldfusion with IPS detections reaching upto 50,000+ unique detections. Users of Adobe ColdFusion are advised to apply patches as per vendor guidelines as soon as possible to mitigate any risk completely, if not already done.
-
January 08, 2024: CVE-2023-38203- Adobe ColdFusion Deserialization of Untrusted Data Vulnerability, was added to CISA KEV list and has been seen to be actively exploited.
-
November 28, 2023: CVE-2023-26347- Another Access Control Bypass vulnerability was announced and Adobe released patches for it.
https://helpx.adobe.com/ca/security/products/coldfusion/apsb23-52.html -
July 20, 2023: Adobe ColdFusion vulnerabilities (CVE-2023-38205, CVE-2023-29298) were added to CISA's KEV catalog.
-
July 19, 2023: Adobe released security updates for ColdFusion versions 2023, 2021 and 2018 to fix (CVE-2023-38205). At the time of the release, Adobe mentioned that CVE-2023-38205 has been exploited in the wild and has been seen in limited attacks. Please note, CVE-2023-38205 was released as a fix for incomplete patch for CVE-2023-29398.
https://helpx.adobe.com/security/products/coldfusion/apsb23-47.html
FortiGuard Cybersecurity Framework
Mitigate security threats and vulnerabilities by leveraging the range of FortiGuard Services.
-
Vulnerability
-
IPS
-
Web App Security
-
IOC
-
Outbreak Detection
-
Threat Hunting
-
Playbook
-
Assisted Response Services
-
Automated Response
-
NOC/SOC Training
-
End-User Training
-
Attack Surface Hardening
-
Vulnerability Management
-
Business Reputation
Threat Intelligence
Information gathered from analyzing ongoing cybersecurity events including threat actors, their tactics, techniques, and procedures (TTPs), indicators of compromise (IOCs), malware and related vulnerabilities.
References
Sources of information in support and relation to this Outbreak and vendor.