MSIL/Crypmod.SB!tr.ransom
 Analysis
Analysis
MSIL/Crypmod.SB!tr.ransom is a generic detection for a Ransomware Crypmod trojan. Since this is a generic detection, this malware may have varying behaviour.
Below are some of its observed characteristics/behaviours:
- This malware may drop any of the following file(s):
- !!!READ_IT!!!.txt : This file is dropped all over the affected hosts drive and will serve as ransom notes.
- Affected files of this Ransomware will use the filenaming format [OriginalFileName.ext].mira.
- Affected victims of this Ransomware are redirected by the attacker via:
- 575913661@qq.com
- recoverymydata@protonmail.com
- mydatarecovery@india.com
- This malware may apply any of the following registry modification(s):
- HKLM\Software\Microsoft\Windows\Currentversion\Run
- XXX_xxxxxxxxxxxxxxxxxx = "%currentpath%\[OriginalMalware].exe" XXX_xxxxxxxxxxxxxxxxxx, where x is any numeric character.
- HKLM\Software\Microsoft\Windows\Currentversion\Run
- Below is an illustration of the malware's Ransom notes:
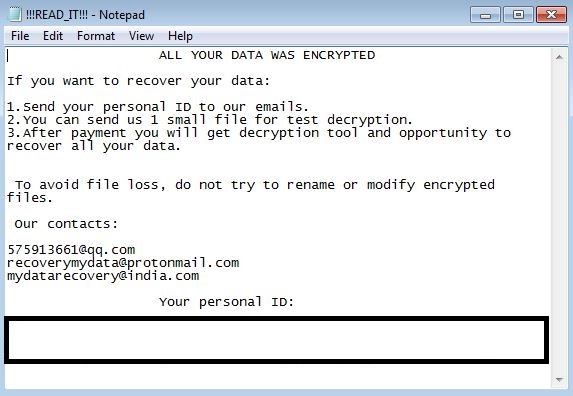
- Figure 1: Ransom notes.
 Recommended Action
Recommended Action
- Make sure that your FortiGate/FortiClient system is using the latest AV database.
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiClient | |
|---|---|
| Extreme | |
| FortiMail | |
| Extreme | |
| FortiSandbox | |
| Extreme | |
| FortiWeb | |
| Extreme | |
| Web Application Firewall | |
| Extreme | |
| FortiIsolator | |
| Extreme | |
| FortiDeceptor | |
| Extreme | |
| FortiEDR |