LNK/Agent.F6C8!tr.dldr
 Analysis
Analysis
LNK/Agent.F6C8!tr.dldr is a generic detection for a LNK / PowerShell Downloader Trojan that installs a potential Locky Ransomware, detected as W32/GenKryptik.AVEL!tr.ransom.
Since this is a generic detection, this malware may have varying behaviour.
Along with W32/GenKryptik.AVEL!tr.ransom, below are some of the observed characteristics/behaviours for this infection:
- This malicious document has an embedded a powershell commandline through a Shortcut link located in %Temp%\.
The powershell LNK then reads a further script obtained from hapce{Removed}.com.
This script in turn will then download the actual Ransomware from any of the following sites:
- hxxp://fgmindi{Removed}.com/HJGdyt73
- hxxp://feigel-fensterba{Removed}.eu/HJGdyt73
- hxxp://euriskosr{Removed}.it/HJGdyt73
- hxxp://gulerci{Removed}.com/HJGdyt73
- hxxp://thennaloperdo{Removed}.net/p66/HJGdyt73
- Below are illustrations of infected document(s):
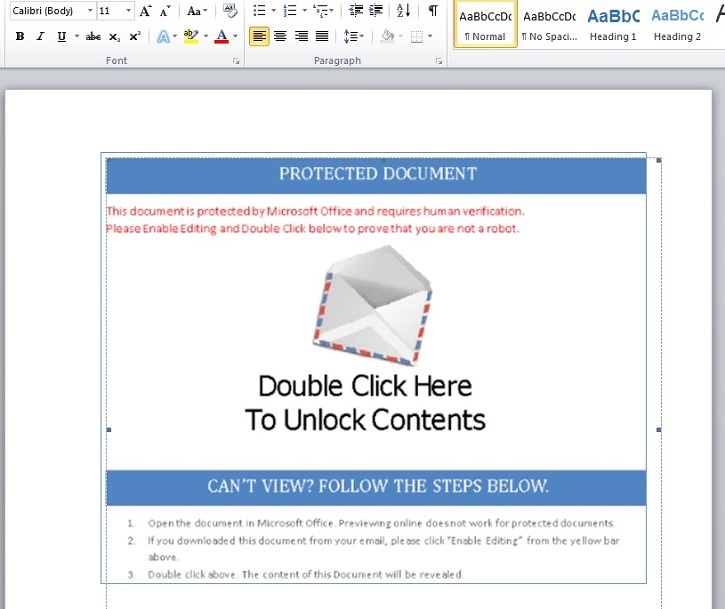
- Figure 1: Infected Document.
 Recommended Action
Recommended Action
- Make sure that your FortiGate/FortiClient system is using the latest AV database.
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiGate | |
|---|---|
| FortiClient | |
| FortiAPS | |
| FortiAPU | |
| FortiMail | |
| FortiSandbox | |
| FortiWeb | |
| Web Application Firewall | |
| FortiIsolator | |
| FortiDeceptor | |
| FortiEDR |