VBA/Agent.86A8!tr.dldr
 Analysis
Analysis
VBA/Agent.86A8!tr.dldr is a generic detection for a type of macro downloader trojan that downloads the Locky ransomware detected as W32/Kryptik.FUJR!tr.
Since this is a generic detection, files that are detected as VBA/Agent.86A8!tr.dldr may have varying behavior.
Along with W32/Kryptik.FUJR!tr below are examples of its observed behavior:
- It downloads the Locky ransomware as the following file:
- undefinedTempundefined[Random].exe : This file is detected as W32/Kryptik.FUJR!tr .
- It adds the ".lukitus" extension to encrypted files.
- It attempts to connect to the following URLs:
- hxxp://zona{Removed}.top/1
- hxxp://baby{Removed}.com/image/flags/1
- hxxp://long{Removed}.com.vn/image/flags/1
- Below is an example of the Ransom notes along with the infected document sample:
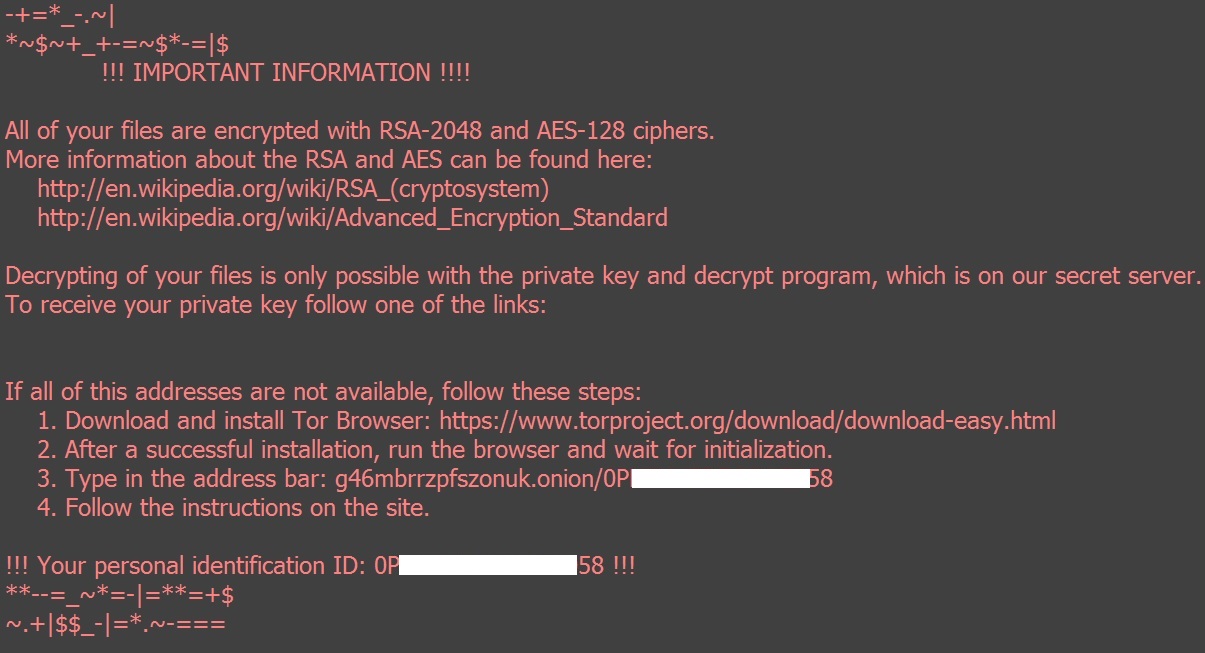
- Figure 1: Ransom notes.
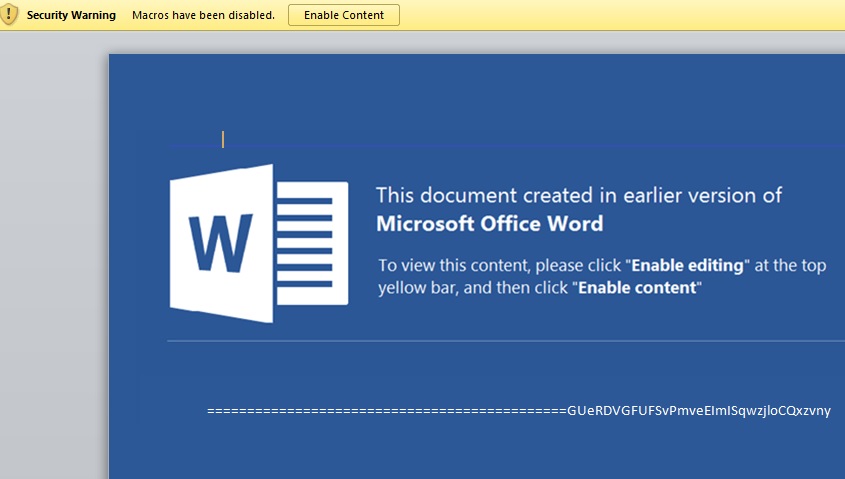
- Figure 2: Infected document.
 Recommended Action
Recommended Action
- Make sure that your FortiGate/FortiClient system is using the latest AV database.
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiClient | |
|---|---|
| Extreme | |
| FortiMail | |
| Extreme | |
| FortiSandbox | |
| Extreme | |
| FortiWeb | |
| Extreme | |
| Web Application Firewall | |
| Extreme | |
| FortiIsolator | |
| Extreme | |
| FortiDeceptor | |
| Extreme | |
| FortiEDR |