Android/SeaWeth.A!tr
 Analysis
Analysis
Android/Seaweth.A!tr is a piece of malware targetting Android mobile phones.
The malicious package comes disguised as a weather application, however in the background connects to a server to receive a premium number to which it sends out SMS messages from the victim's phone.
Technical Details
The main application is called "Seaweed Weather Forecast"(in Chinese) (ref Fig1) and comes in the package "com.picvision.seaweedweather"
Fig1 : Seaweed Weather Forecast application Icon
When the application is launched, the user is asked to choose a city from a list as seen in Fig2
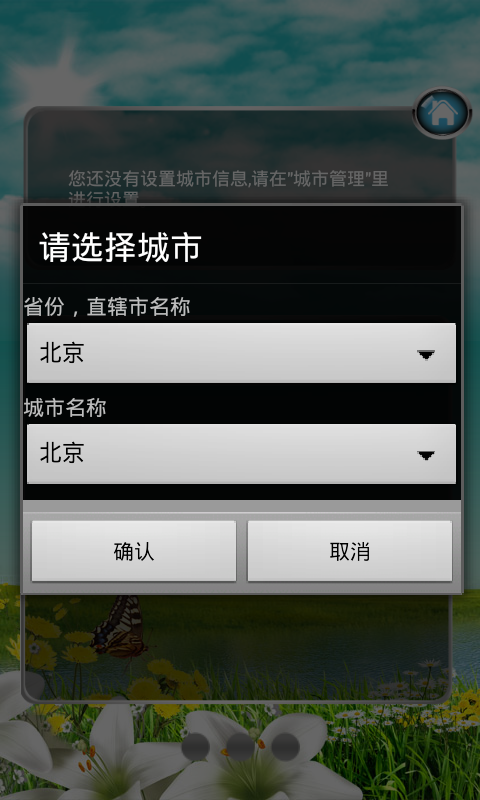
Fig2 : Seaweed Weather Main Application
Depending upon the user's selection, the weather of the particular city is displayed. The legitimate activity of the application ends here.
Next, it sends an HTTP request to the URL
hxxp://[REMOVED]/weatherServer/GetProducts.jsp?version=2.0.0&gender="+xand saves the response to a file text.xml.
This response contains several advertisements shown to the user as seen in Fig3.
Fig3 : Advertisements
Clicking on each advertisement results in further internet usage resulting in possible losses for the user.
Finally, it sends an HTTP request to the URL
hxxp://[REMOVED]/getSMSnumber.jspThe server responds with a premium number.
The infected phone then sends out an SMS message to this received number with the content
"imsi:" + IMSI + ",software:SeaweedWeatherV1.0.0_FREE_AD1.5_AllSizes"where IMSI = IMSI number of the infected phone.
The trojan also checks for updates and installs them depending upon the response received from
hxxp://[REMOVED]/softwareupdatecheck.jsp?imsi=" + IMSI + "&software=SeaweedWeatherV1.0.0_FREE_AD1.5_AllSizes"
Permissions required by the application:
- INTERNET
- RECEIVE_SMS
- READ_PHONE_STATE
- SEND_SMS
- WRITE_EXTERNAL_STORAGE
- MOUNT_UNMOUNT_FILESYSTEMS
- READ_CALENDAR
- WRITE_CALENDAR
 Recommended Action
Recommended Action
- FortiGate Systems
- Check the main screen using the web interface for your FortiGate unit to ensure that the latest AV/NIDS database has been downloaded and installed on your system - if required, enable the "Allow Push Update" option.
FortiClient Systems
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiGate | |
|---|---|
| Extreme | |
| FortiClient | |
| Extended | |
| FortiMail | |
| Extended | |
| FortiSandbox | |
| Extended | |
| FortiWeb | |
| Extended | |
| Web Application Firewall | |
| Extended | |
| FortiIsolator | |
| Extended | |
| FortiDeceptor | |
| Extended | |
| FortiEDR |