Android/RogueSPPush.A!tr
 Analysis
Analysis
Android/RogueSPPush.A!tr belongs to a family of Trojans whose main goal is to
automatically subscribe the victim to a mobile value-added service.
The subscription is done automatically and without the victim's consent.
The victim is charged for the service it is subscribed to.
This variant poses as a Chinese love application, and automatically sends
a subscription confirmation SMS for the related value-added service.
The confirmation SMS is sent without user's consent.
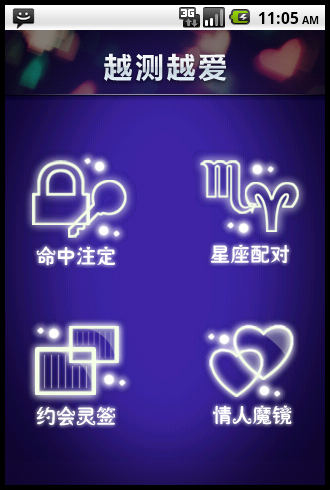
Figure 1. Splash screen for Android/RogueSPPush love application
Technical Details
The malware registers a SMS receiver with a high priority to ensure it handles the SMS before any other receiver.
It retrieves the originating phone number of the SMS and the SMS body.
If the body of the SMS contains given keywords ("supermarket" in Chinese for instance), it automatically replies with a SMS containing body "Y". In that case, "Y" is assumed to mean "yes", and automatically subscribe the victim to that service.
Additionally, if the malware receives an SMS from a phone number beginning with 10086 or 10658 and whose body mentions the malware's application name, As a matter of fact, 10086 is used by a major Chinese operator to inform an end-user of Service Providers he/she is subscribing to.
Once the victim has unwillingly subscribed, the malware shows the capability of sending other SMS. In particular, it splits their bodies to 70 characters max.
 Recommended Action
Recommended Action
- FortiGate Systems
- Check the main screen using the web interface for your FortiGate unit to ensure that the latest AV/NIDS database has been downloaded and installed on your system - if required, enable the "Allow Push Update" option.
FortiClient Systems
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiGate | |
|---|---|
| Extended | |
| FortiClient | |
| Extreme | |
| FortiAPS | |
| FortiAPU | |
| FortiMail | |
| Extreme | |
| FortiSandbox | |
| Extreme | |
| FortiWeb | |
| Extreme | |
| Web Application Firewall | |
| Extreme | |
| FortiIsolator | |
| Extreme | |
| FortiDeceptor | |
| Extreme | |
| FortiEDR |
Version Updates
| Date | Version | Detail |
|---|---|---|
| 2023-03-06 | 91.01181 |