W32/GuLoader.VHIM!tr
 Analysis
Analysis
W32/GuLoader.VHIM!tr is a generic detection for a trojan.
Since this is a generic detection, malware that are detected as W32/GuLoader.VHIM!tr may have varying behaviour.
Below are some of its observed characteristics/behaviours:
- This malware drops the file %CurrentUser%\Roaming\Install\Host.exe and is currently detected as W32/GuLoader.VHIM!tr
- This malware Guloader will try to download the encrypted binary from some famous free cloud storage (one of our tests indicates it uses google drive), and could perform simple xor decryption upon the downloaded file.
- This malware also has the capability to copy itself and propagate by attaching its code to other programs or files.
- The encrypted binary is a type of malware that performs activities without the user’s knowledge. These activities commonly include :
- establishing remote access connections
- capturing keyboard input
- collecting system information
- downloading/uploading files
- dropping other malware into the infected system
- performing denial-of-service (DoS) attacks
- and running/terminating processes
- This malware is VB compiled.
- The malware appears to check if its running on a virtualized environment and displays the following message
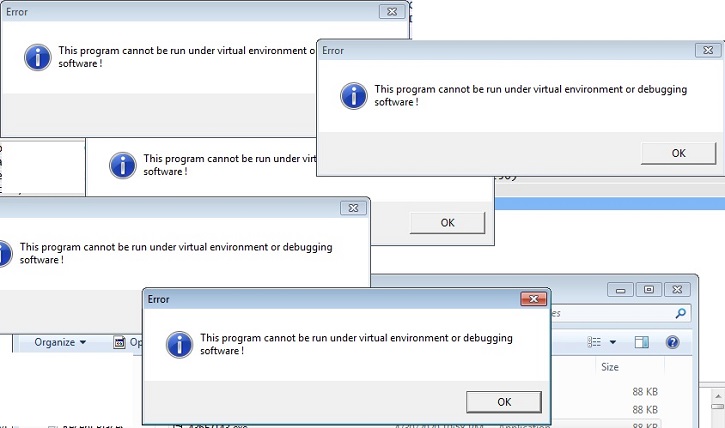
- Figure 1: Malware Prompt.
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- NetWire = "%CurrentUser%\Roaming\Install\Host.exe"
- HKEY_CURRENT_USER\Software\NetWire
This registry keeps a tally of the malwares installation date.
 Recommended Action
Recommended Action
- Make sure that your FortiGate/FortiClient system is using the latest AV database.
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiGate | |
|---|---|
| Extended | |
| FortiClient | |
| FortiMail | |
| FortiSandbox | |
| FortiWeb | |
| Web Application Firewall | |
| FortiIsolator | |
| FortiDeceptor | |
| FortiEDR |