MSIL/CryptoJoker.C!tr.ransom
 Analysis
Analysis
MSIL/CryptoJoker.C!tr.ransom is a generic detection for a Ransomware CryptoJoker trojan. Since this is a generic detection, this malware may have varying behaviour.
Below are some of its observed characteristics/behaviours:
- This malware may drop any of the following file(s):
- CryptoJoker Recovery Information.txt : This file is dropped on the desktop and will serve as the ransom note.
- This Ransomware was observed to infect all the files in C:\Users\%UserName% with %UserName% being the user that the ransomware was run in.
- Affected files of this Ransomware will use the filenaming format OriginalFileName.ext. partially.cryptojoker, where italic strings are replaced.
- Affected victims of this Ransomware are directed to pay the ransom to the malware author's bitcoin address.
- Below is an illustration of the malware's Ransom note:
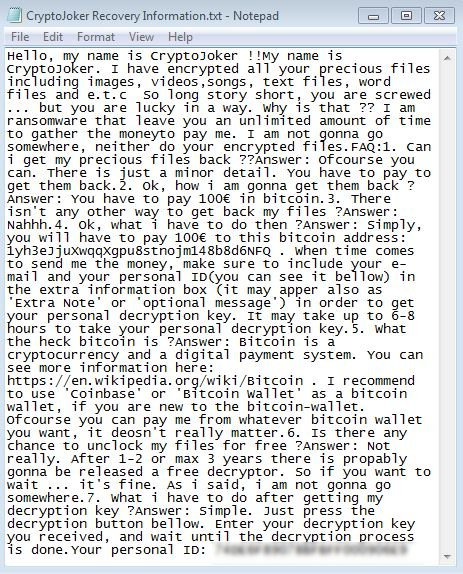
- Figure 1: Ransom note.
 Recommended Action
Recommended Action
- Make sure that your FortiGate/FortiClient system is using the latest AV database.
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiGate | |
|---|---|
| Extended | |
| FortiClient | |
| Extreme | |
| FortiAPS | |
| FortiAPU | |
| FortiMail | |
| Extreme | |
| FortiSandbox | |
| Extreme | |
| FortiWeb | |
| Extreme | |
| Web Application Firewall | |
| Extreme | |
| FortiIsolator | |
| Extreme | |
| FortiDeceptor | |
| Extreme | |
| FortiEDR |