W32/HydraCrypt.C!tr.ransom
 Analysis
Analysis
W32/HydraCrypt.C!tr.ransom is a generic detection for a Ransomware HydraCrypt trojan.
Since this is a generic detection, this malware may have varying behaviour.
Below are some of its observed characteristics/behaviours:
- This malware may drop any of the following file(s):
- HELP_DECRYPT_YOUR_FILES.TXT : This file is dropped all over the affected hosts drive and will serve as ransom notes.
- Affected files of this Ransomware may use any of the following filenaming formats:
- {OriginalFileName.Ext}_[id]_email_enc5@dr.com_.scl
- XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX.WORK, where X is any uppercase alphanumeric character.
- This malware was also observed to affect/encrypt files located on shared drives within the same subnet.
- Affected victims of this Ransomware are redirected by the attacker via:
- enc5@usa.com
- enc5@dr.com
- enc5r@usa.com
- encr5r@dr.com
- worknow@keemail.me
- worknow@protonmail.com
- worknow8@yandex.com
- worknow9@yandex.com
- worknow@techie.com
- alpha2018a@aol.com
- Below is an illustration of the malware's Ransom notes:
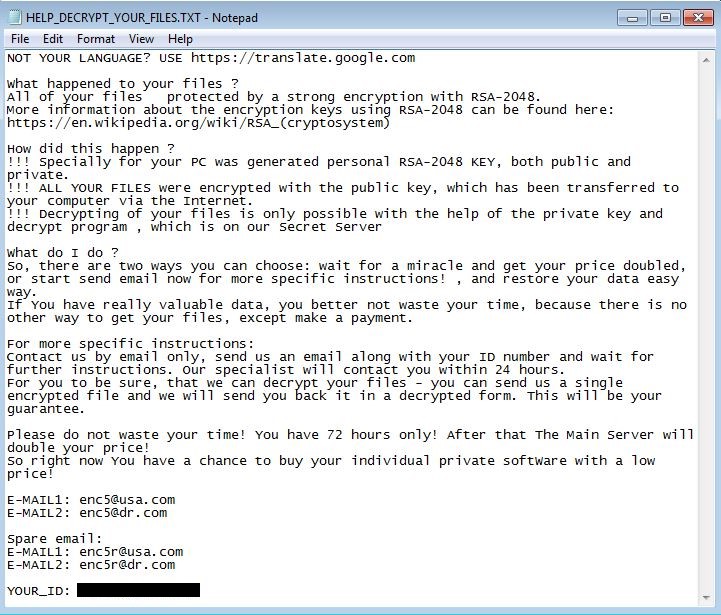
- Figure 1: A screenshot of how the Ransom note may appear.
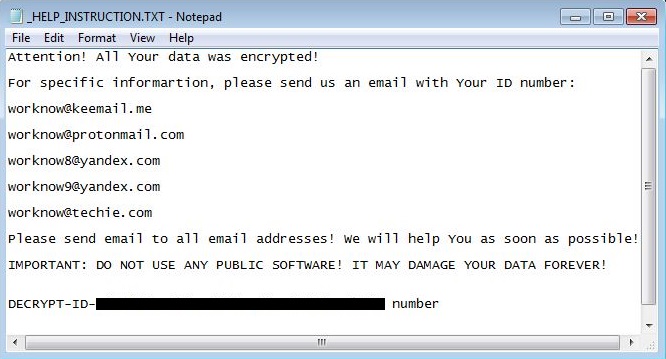
- Figure 2: A screenshot of how the Ransom note may appear.
 Recommended Action
Recommended Action
- Make sure that your FortiGate/FortiClient system is using the latest AV database.
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiGate | |
|---|---|
| FortiClient | |
| FortiAPS | |
| FortiAPU | |
| FortiMail | |
| FortiSandbox | |
| FortiWeb | |
| Web Application Firewall | |
| FortiIsolator | |
| FortiDeceptor | |
| FortiEDR |
Version Updates
| Date | Version | Detail |
|---|---|---|
| 2023-03-27 | 91.01812 | |
| 2021-12-28 | 89.08183 | |
| 2020-10-20 | 81.23000 | Sig Updated |
| 2020-07-21 | 79.05400 | Sig Updated |
| 2019-06-18 | 69.35000 | Sig Updated |
| 2019-04-12 | 67.75300 | Sig Updated |
| 2019-04-01 | 67.48700 | Sig Updated |
| 2019-04-01 | 67.48600 | Sig Updated |
| 2019-03-26 | 67.33800 | Sig Updated |
| 2019-03-11 | 66.98200 | Sig Updated |