W32/LockerGoga.9FE6!tr.ransom
 Analysis
Analysis
W32/LockerGoga.9FE6!tr.ransom is a detection for a Ransomware trojan.
Below are some of its observed characteristics/behaviours:
- This malware may drop any of the following file(s):
- %Desktop%\README_LOCKED.txt : This file will serve as ransom notes.
- %Temp%\[RandomFileName].exe : This file is a copy of the original malware itself.
- During the time of our tests this malware failed to encrypt files, but the malware does indicate that it seems trying to locate external drives, a common behaviour for Ransomware.
- The malware also moves/deletes itself after initial execution.
- Affected victims of this Ransomware are redirected by the attacker via:
- SuzuMcpherson@protonmail.com
- AsuxidOruraep1999@o2.pl
- Below is an illustration of the malware's Ransom notes and chracteristics:
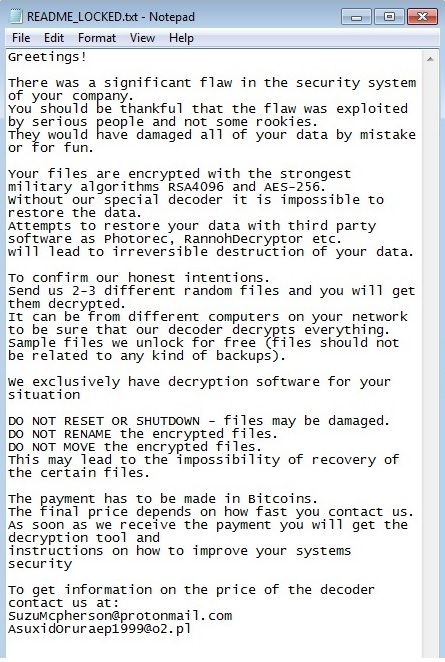
- Figure 1: Ransom note README_LOCKED.txt.
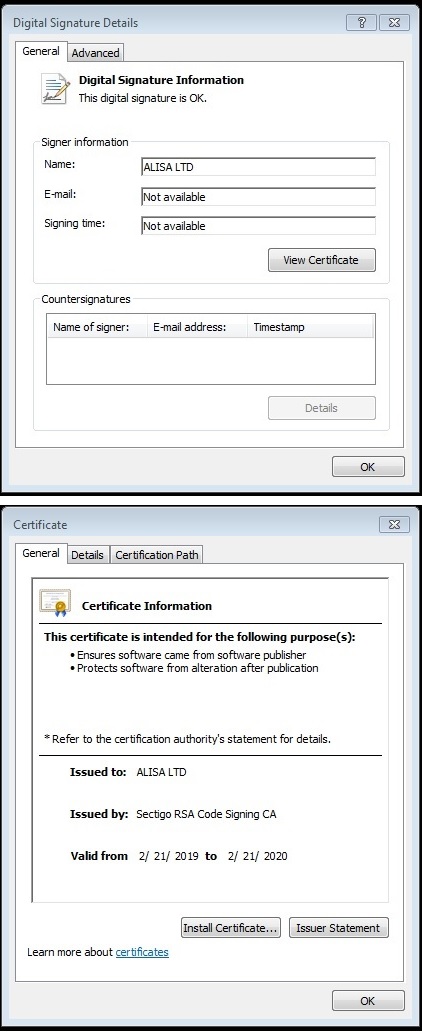
- Figure 2: One unique feature of this malware is its presence of Digital Signature.
 Recommended Action
Recommended Action
- Make sure that your FortiGate/FortiClient system is using the latest AV database.
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiGate | |
|---|---|
| Extended | |
| FortiClient | |
| FortiMail | |
| FortiSandbox | |
| FortiWeb | |
| Web Application Firewall | |
| FortiIsolator | |
| FortiDeceptor | |
| FortiEDR |
Version Updates
| Date | Version | Detail |
|---|---|---|
| 2019-03-08 | 66.90900 | Sig Added |