W32/Jigsaw.M!tr.ransom
 Analysis
Analysis
W32/Jigsaw.M!tr.ransom is a detection for a Jigsaw Ransomware trojan.
Below are some of its observed characteristics/behaviours:
- This malware may drop any of the following file(s):
- %Appdata%\Frfx\firefox.exe : This file is the copy of the malware itself.
- %Appdata%\Drpbx\Drpbx.exe : This file is the copy of the malware itself.
- %Appdata%\Roaming\Adb\AdobeFlash.exe : This file is the copy of the malware itself.
- %Appdata%\System32Work\EncryptedFileList.txt : This file contains the list of the encrypted files.
- %Appdata%\System32Work\Address.txt : This file contains the bitcoin wallet potentially owned by the attacker.
- %Appdata%\Roaming\svchost.exe : One variant of this ransomware drops this file. This file is the copy of the original malware itself.
- Affected files of this Ransomware will use the filenaming format [OriginalFileName].fun or [OriginalFileName].mer or [OriginalFileName.Ext].data or [OriginalFileName.Ext].venom
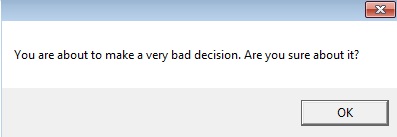
- This Ransomware deletes 1000 files if the victim restarts the affected system.
- The following registry modifications are applied:
- HKCU\Software\Microsoft\Windows\Currentversion\Run
- firefox.exe = %Appdata%\Frfx\firefox.exe
- svchost.exe = %Appdata%\Roaming\svchost.exe
- HKCU\Software\Microsoft\Windows\Currentversion\Run
- Below is an illustration of the malware's Ransom notes:
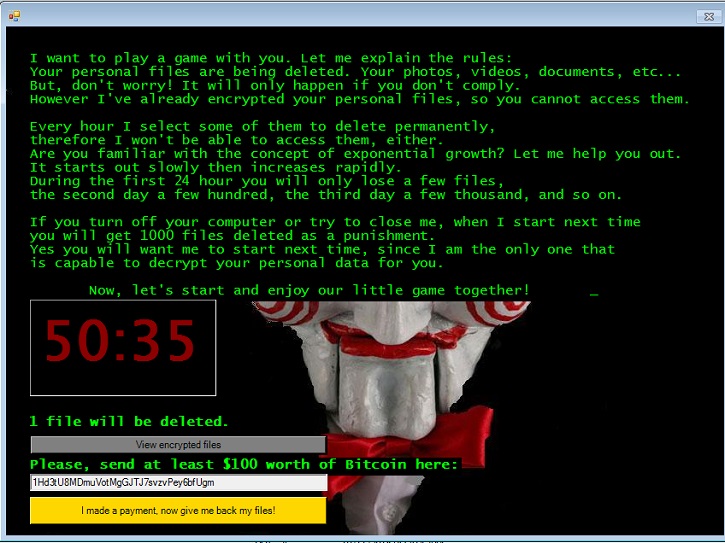
- Figure 1: Ransom notes.
- Below is a prompt that displays when the victim attempts to reboot the system:
- Figure 2: Message Prompt.
|
 Recommended Action
Recommended Action
- Make sure that your FortiGate/FortiClient system is using the latest AV database.
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiClient | |
|---|---|
| Extreme | |
| FortiMail | |
| Extreme | |
| FortiSandbox | |
| Extreme | |
| FortiWeb | |
| Extreme | |
| Web Application Firewall | |
| Extreme | |
| FortiIsolator | |
| Extreme | |
| FortiDeceptor | |
| Extreme | |
| FortiEDR |