Elf/Agent.1731!tr
 Analysis
Analysis
Elf/Agent.1731!tr is a detection for an Elf trojan.
This detection has been directly associated with the VPNFilter attack.
Below are some of its observed behaviours/chracteristics:
- It involves a multi stage attack where an x86 Elf binary downloads another x86 Elf binary from either photobucket.com or toknowall.com, afterwhich implements the main payloads. The malware assumes itself as already running within the affected appliance/device. The initial method on how to place the malware itself onto an affected device is still not clear at the time of this writing, and has been speculated to possibly utilize a known/unknown vulnerability.
- Below are some of the noticeable quick analysis we did on the malware's x86 Elf Binary :
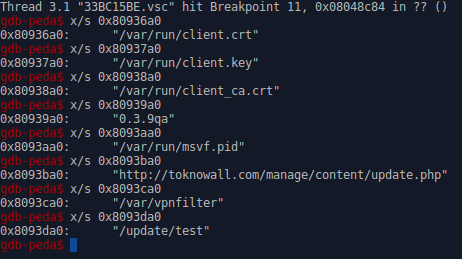
- Figure 1: Decoded strings indicating the dropped files and the URL it attempts to connect to.
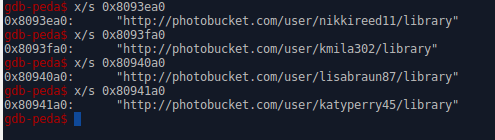
- Figure 2: URLs where the malware may intend to extract EXIF metadata for additional server IP Addresses .
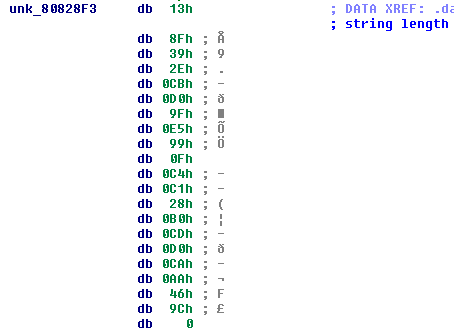
- Figure 3: Original Encoded strings from malware body.
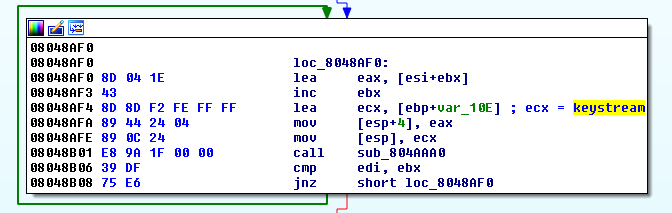
- Figure 4: RC4 Decryption routine.
 Recommended Action
Recommended Action
- Make sure that your FortiGate/FortiClient system is using the latest AV database.
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiGate | |
|---|---|
| FortiClient | |
| FortiAPS | |
| FortiAPU | |
| FortiMail | |
| FortiSandbox | |
| FortiWeb | |
| Web Application Firewall | |
| FortiIsolator | |
| FortiDeceptor | |
| FortiEDR |