W32/GenKryptik.BAPN!worm
 Analysis
Analysis
W32/GenKryptik.BAPN!worm is a generic detection for a trojan. Since this is a generic detection, malware that are detected as W32/GenKryptik.BAPN!worm may have varying behaviour.
Below are examples of some of these behaviours:
- This malware may drop any of the following file(s):
- undefinedSystemRootundefined\M-XXXXXXXXXXXXXXXXXXXXXXXXXXXXX\winmgr.exe : where X is any numerical character, this file is a copy of the original malware itself.
- undefinedTempundefined\[Random].bat : This file appears to be a text file only, possibly intended to delete the original malware itself.
- undefinedAppDataundefined\winmgr.txt : This file is non-malicious text file.
- undefinedInternet_Cacheundefined\mi.exe : This file is detected as W32/GenKryptik.BAPN!worm.
- undefinedInternet_Cacheundefined\b20.exe : This file is detected as W32/GenKryptik.BAPN!worm.
- undefinedTempundefined\[Random].exe : This file is detected as W32/GenKryptik.BAPN!worm.
- undefinedTempundefined\[Random] : This file is detected as W32/GenKryptik.BAPN!worm.
- undefinedAppDataundefined\wincfg.exe : This file is detected as W32/GenKryptik.BAPN!worm.
- This malware may connect to any of the following remote sites(s):
- 22{Removed}.181.87.80
- hxxp://14{Removed}.135.152.86/mi.exe
- hxxp://ww{Removed}.murphysisters.org/images/mi.exe
- hxxp://ww{Removed}.murphysisters.org/images/b20.exe
- This malware may have bitcoin mining component and executes an instance of itself with a parameter -o monerohash.com:3333 -u [EncryptedString] -p x -k --donate-level=1 -t 2 .
- This malware may also creates a Task Schedule for itself displayed as Adasdsadas3id and is expected to run every minute serving as auto prevalence.
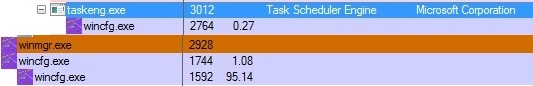
- Figure 1: malware process.
- This malware may apply any of the following registry modification(s):
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\Currentversion\Run
- Microsoft windows manager = undefinedSystemRootundefined\M-XXXXXXXXXXXXXXXXXXXXXXXXXXXXX\winmgr.exewinmgr.exe
- HKEY_CURRENT_USER\Software\Microsoft\Windows\Currentversion\Run
- Microsoft windows manager = undefinedSystemRootundefined\M-XXXXXXXXXXXXXXXXXXXXXXXXXXXXX\winmgr.exe\winmgr.exe
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\Currentversion\Run
- This malware also may affect and intend to spread via external drive by dropping the following files:
- autorun.inf
- DeviceConfigManager.vbs
- _\DeviceConfigManager.exe
- .lnk
- The original copy of the malware may be deleted after execution.
 Recommended Action
Recommended Action
- Make sure that your FortiGate/FortiClient system is using the latest AV database.
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiGate | |
|---|---|
| Extended | |
| FortiClient | |
| FortiMail | |
| FortiSandbox | |
| FortiWeb | |
| Web Application Firewall | |
| FortiIsolator | |
| FortiDeceptor | |
| FortiEDR |