JS/Agent.5A56!tr
 Analysis
Analysis
JS/Agent.5A56!tr is a generic detection for a Javascript Downloader trojan for a variant of Locky Ransomware detected as W32/Locky.B703!tr.
Since this is a generic detection, malware that are detected as JS/Agent.5A56!tr may have varying behaviour.
Along with W32/Locky.B703!tr below are some of the observed behaviours of this infection:
- This malware will cause to drop the following files:
- undefinedUserundefined\Desktop\lukitus.bmp : This an image of the ransom notes.
- undefinedUserundefined\Desktop\lukitus.htm : This is the ransom notes.
- lukitus-[Random].htm : This file is another ransom note dropped all over the affected hosts.
- This malware usually downloads a file from a remote site enlisted below then drops it as undefinedAppDataundefined\[Random].exe then executes it, afterwhich it then enlist currently running processes.
- hookerdeepseafishin{Removed}.com/pututfi.exe
- hxxp://ww{Removed}.universodeljuguete.com/eusukll.exe
- hxxp://babmitontwronse{Removed}.info/eroorrrs
- hxxp://etforhartoha{Removed}.info/af/uyfehjg.exe
- Files affected by this malware will use the a filenaming format XXXXXXXX-XXXX-XXXX-XXXXXXXX-XXXXXXXXXXXX.lukitus, where X is hexadecimal character.
- Below are some of the illustrations of the Ransomware notes:
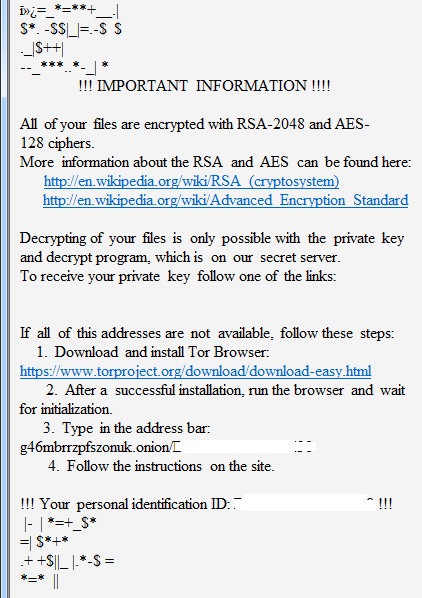
- Figure 1: Ransom notes.
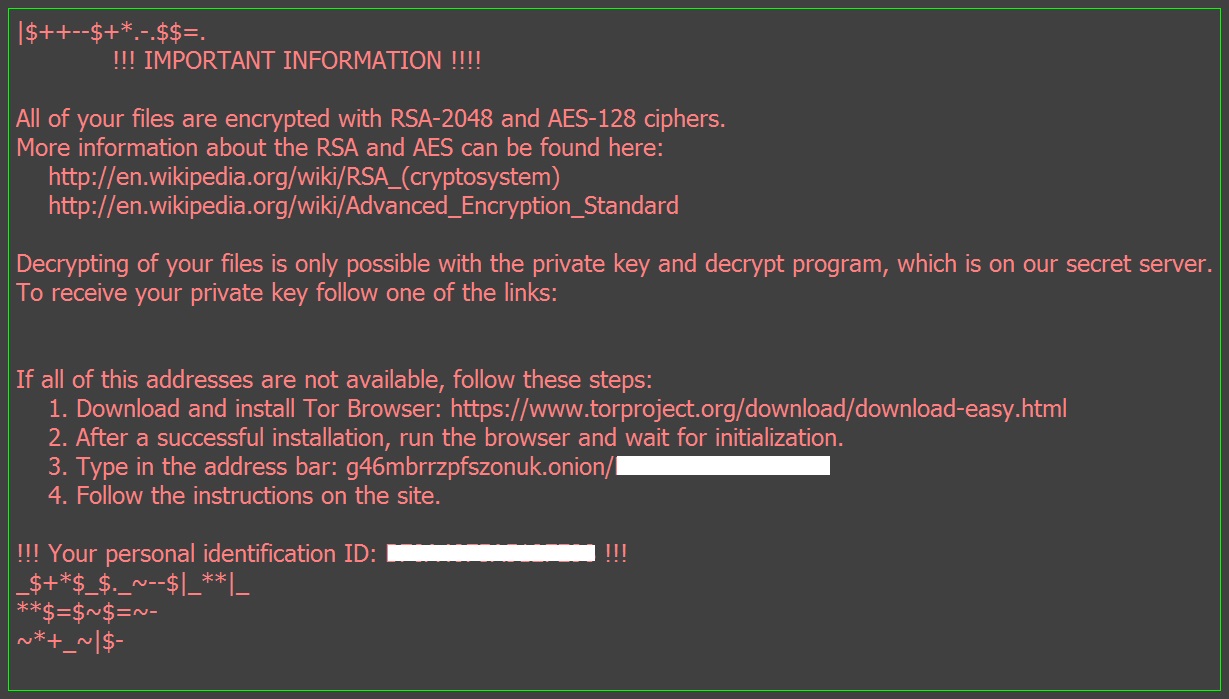
- Figure 2: Ransom notes.
 Recommended Action
Recommended Action
- Make sure that your FortiGate/FortiClient system is using the latest AV database.
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiClient | |
|---|---|
| Extreme | |
| FortiMail | |
| Extreme | |
| FortiSandbox | |
| Extreme | |
| FortiWeb | |
| Extreme | |
| Web Application Firewall | |
| Extreme | |
| FortiIsolator | |
| Extreme | |
| FortiDeceptor | |
| Extreme | |
| FortiEDR |