W32/Agent.AF!tr
 Analysis
Analysis
W32/Agent.AF!tr is a very generic detection for a trojan.
Since this is a generic detection, malware that are detected as W32/Agent.AF!tr may have varying behaviour.
Below are examples of some of these characteristics/behaviours:
- This detection is not based on any specific malware family and would catch a wide array of malware.
- Some malware that belong to this detection are AutoIt based.
- Some malware that belong to this detection may utilize powershell command line.
- Some instances of this malware may drop any of the following file(s):
- undefinedAllUsersProfileundefined\taskhos.exe : This file is a copy of the original malware itself.
- undefinedUserProfileundefined\[Random]\[Random].vbs : This file is detected as VBS/Runner.NCL!tr.
- Some instances of this malware may apply any of the following registry modification(s):
- HKEY_CURRENT_USER\Software\Microsoft\Windows\Currentversion\Runonce
- [Random] = undefinedUserProfileundefined\[Random]\[Random].vbs
- HKEY_CURRENT_USER\Software\Microsoft\Windows\Currentversion\Runonce
- Some instances may drop the following files:
- Opens a photo as a decoy. This file is dropped as undefinedsystemrootundefined\system32\angie.jpg
- undefinedsystemrootundefined\system32\msjvms32.exe : This file is a copy of the original malware itself.
- Below are some of user interface or infections caught during our tests:

- Figure 1: Running malware process.
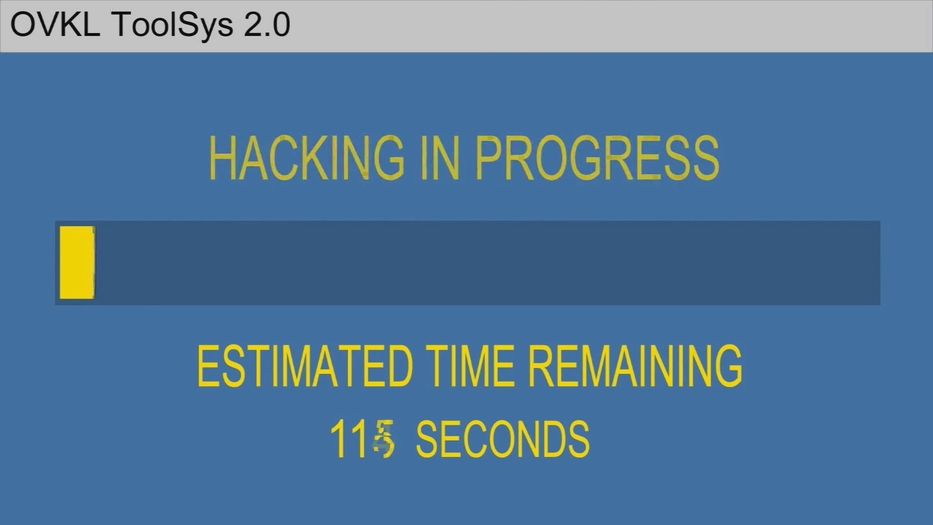
- Figure 2: Malware payload.
 Recommended Action
Recommended Action
- Make sure that your FortiGate/FortiClient system is using the latest AV database.
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiGate | |
|---|---|
| Extended | |
| FortiClient | |
| FortiMail | |
| FortiSandbox | |
| FortiWeb | |
| Web Application Firewall | |
| FortiIsolator | |
| FortiDeceptor | |
| FortiEDR |