Android/DroidKungFu.G!tr
 Analysis
Analysis
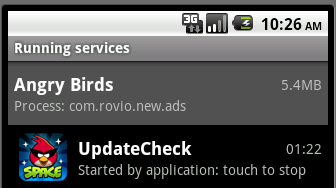
Android/DroidKungFu.G!tr infects Android phones through
trojaned legitimate applications, such as the new Angry
Birds Space.

Android/DroidKungFu.G!tr is a variant of
Android/DroidKungFu.A!tr.
The difference with the A variant are as follows:
- Package name and hierarchy (now located under the path com.neworld.demo)
- Command and Control Server URLS (same URLs as Android/DroidKungFu.F!tr)
- C&C commands and URLs are implemented natively (like the Android/DroidKungFu.E!tr variant)
The malware first starts a service called UpdateCheck.
This service will extract 2 ELF files from a legitimate and functionnal JPEG picture called mylogo.jpg, and execute them.
The 1st extracted file is the GingerBreak exploit used to gain root access on the phone. With the exploit embedded in the application, the malware no longer depends on user interaction to gain root permissions.
Android phones which haven't been patched against the security hole exploited by GingerBreak are vulnerable to an attack. The exploit is known to work on Android Honeycomb (3.x.x), Android Gingerbread (2.3.x), Android Froyo (2.2) and Android Eclair (2.1).
Once root permissions are gained, the trojan drops the 2nd payload.
Just like the Android/DroidKungFu.F!tr variant, Android/DroidKungFu.G!tr obfuscates strings in the native code with a bitwise NOT.
Its first task is to decrypt all those strings and it will try to copy itself as:
- /system/bin/debuggerd
- /system/bin/vold
- /system/bin/rm
- /system/bin/move
- /system/bin/mount
- /system/bin/ifconfig
- /system/bin/chown
- /system/bin/dhcpd
- /system/bin/installd
This second payload is responsible for communication with the C&C server to install packages and to push URLs to be displayed in the web browser.
It uses the same URLs as Android/DroidKungFu.F!tr variant.
There are 3 C&C servers URLs:
- http://[CENSORED]new.com:8511/search/
- http://[CENSORED]go8.com:8511/search/
- http://[CENSORED]968.com:8511/search/
 Recommended Action
Recommended Action
- FortiGate Systems
- Check the main screen using the web interface for your FortiGate unit to ensure that the latest AV/NIDS database has been downloaded and installed on your system - if required, enable the "Allow Push Update" option.
FortiClient Systems
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiClient | |
|---|---|
| Extreme | |
| FortiMail | |
| Extreme | |
| FortiSandbox | |
| Extreme | |
| FortiWeb | |
| Extreme | |
| Web Application Firewall | |
| Extreme | |
| FortiIsolator | |
| Extreme | |
| FortiDeceptor | |
| Extreme | |
| FortiEDR |