MSOffice/Reminder.EOP!tr
 Analysis
Analysis
MSOffice/Reminder.EOP!tr is a generic detection for a trojan. Since this is a generic detection, malware that are detected as MSOffice/Reminder.EOP!tr may have varying behaviour.
Below are some of its observed characteristics/behaviours:
- This malware is associated with the Microsoft Outlook outbreak and involves the CVE-2023-23397 vulnerability which allows privilege escalation. This signifies that when the vulnerability is exploited, the application can get permissions or privileges that are not usually accessible to it.
- This elevated privilege in this instance might provide the attacker access to the victim's password hashes.
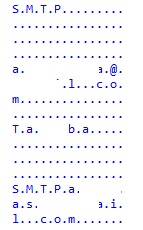
- MSOffice/Reminder.EOP!tr delivers a customized message to a user that tries to compromise the user's mailbox.The malware may perform malicious actions such as a relay attack.
- Below are some of the sites the malware attemps to connect to:
- 172.2[Removed].54/f[Removed]ar
- This malware has been associated with the following third party article/advisory.
https://nvd.nist.gov/vuln/detail/CVE-2023-23397 https://www.cvedetails.com/cve/CVE-2023-23397/
|
|
|
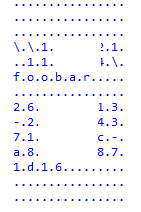
- Md5: eadb4b16755ac36aa9f4a85ebf23fd4c
Sha256: d544d82998bf9955610fe2b2163913c4ea4e6b51ef44e38fbe3f22d835ce58e5 - Md5: d0e6c5c888ff0baa7db12c776617112d
Sha256: 8ccc1c2bc251b7ebbe8ad001e9e9093bc29ebe8652c43b2f3cfc74bb53b10554 - Md5: 30c814ab748f41221006a8d5d8d095a3
Sha256: 6126e5de0d64e8b6da8e03c25b542a1d6a316413a8b364e3c9080f1ab10a2dec - Md5: d668a86587d579a2f8bacc45dcb2024a
Sha256: b33a0eb265d4679a429e9551b76e3ffbd5c4dca39ec50a6af1cda7c49fd14771 - Md5: f60350585fbfc5dc968f45c6ef4e434d
Sha256: 7fb7a2394e03cc4a9186237428a87b16f6bf1b66f2724aea1ec6a56904e5bfad
 Outbreak Alert
Outbreak Alert
CVE-2023-23397 is a critical elevation of privilege (EoP) vulnerability in Microsoft Outlook. It is a zero-touch exploit, meaning the security flaw requires no user interaction to be abused. All supported versions of Microsoft Outlook for Windows are affected including other versions of Microsoft Outlook such as Android, iOS, Mac, as well as Outlook on the web.
 Recommended Action
Recommended Action
- Make sure that your FortiGate/FortiClient system is using the latest AV database.
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiGate | |
|---|---|
| FortiClient | |
| FortiAPS | |
| FortiAPU | |
| FortiMail | |
| FortiSandbox | |
| FortiWeb | |
| Web Application Firewall | |
| FortiIsolator | |
| FortiDeceptor | |
| FortiEDR |