W32/DearCry.OGE!tr.ransom
 Analysis
Analysis
W32/DearCry.OGE!tr.ransom is a generic detection for a Ransomware DearCry trojan.
Since this is a generic detection, this malware may have varying behaviour.
Below are some of its observed characteristics/behaviours:
- This malware may drop any of the following file(s):
- readme.txt : This file is dropped all over the affected hosts drive and will serve as ransom notes.
- Affected files of this Ransomware will use the filenaming format [OriginalFileName.Ext].CRYPT .
- The malware may target files with the following extensions:
- Python files source codes.
- Extesion Names: TIF .TIFF .PDF .XLS .XLSX .XLTM .PS .PPS .PPT .PPTX .DOC .DOCX .LOG .MSG .RTF .TEX .TXT .CAD .WPS .EML .INI .CSS .HTM .HTML .XHTML .JS .JSP .PHP .KEYCHAIN .PEM .SQL .APK .APP .BAT .CGI .ASPX .CER .CFM .C .CPP .GO .CONFIG.CSV .DAT .ISO .PST .PGD .7Z .RAR .ZIP .ZIPX .TAR .PDB .BIN .DB .MDB .MDF .BAK .LOG .EDB .STM .DBF .ORA
- EXEcutable files .exe
- This malware was also observed to affect/encrypt files located on shared drives.
- Below is an illustration of the malware's Ransom notes:
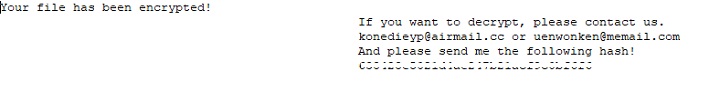
- Figure 1: Ransom Notes.
- Following are some of the near/exact IOCs/file hash associated with this detection:
- 0e55ead3b8fd305d9a54f78c7b56741a
- 6be28a4523984698e7154671f73361bf
- 9f05994819a3d8c1a3769352c7c39d1d
- c6eeb14485d93f4e30fb79f3a57518fc
- cdda3913408c4c46a6c575421485fa5b
 Outbreak Alert
Outbreak Alert
Following initial compromise of the MS Exchange system, the attacker can execute the primary objective. From monitoring these incidents, a new family of ransomware has been detected. The threat is known as DoejoCrypt or DearCry.
 Recommended Action
Recommended Action
- Make sure that your FortiGate/FortiClient system is using the latest AV database.
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
- Our FortiSandbox solution can flag this Ransomware please check this sample report on W32/DearCry.OGE!tr.ransom.
 Telemetry
Telemetry
Detection Availability
| FortiGate | |
|---|---|
| Extreme | |
| FortiClient | |
| Extended | |
| FortiMail | |
| Extended | |
| FortiSandbox | |
| Extended | |
| FortiWeb | |
| Extended | |
| Web Application Firewall | |
| Extended | |
| FortiIsolator | |
| Extended | |
| FortiDeceptor | |
| Extended | |
| FortiEDR |