Android/SMSMngr.A!tr.spy
 Analysis
Analysis
Android/SmsMngr.A!tr.spy is a piece of malware targetting Android mobile phones.
The malicious package comes disguised as a "social CultureNetwork Online Multiplex" application called "Culture Land". However, in the background, it leaks infected phone's information such as IMSI and phone number and received SMS message contents to the attacker's server. In response, the attacker's server can send commands to the infected phone enabling it to perform functions such as deleting, modifying forwarding SMS messages present in the inbox.
The main application is called "Culture Land"(ref Fig1) and comes in the package "com.scott.crash.CrashApplication"
![]()
Fig1 : Culture Land Icon
Upon installation, a POST request is sent to
hxxp://[REMOVED]2580.com/send_sim_no.phpwith the parameters
- mobile_no : [VICTIM's PHONE NUMBER]
- datetime : [CURRENT DATE IN FORMAT "yyyy-MM-dd"]
When the application is launched, the user sees a screen as seen in Fig2
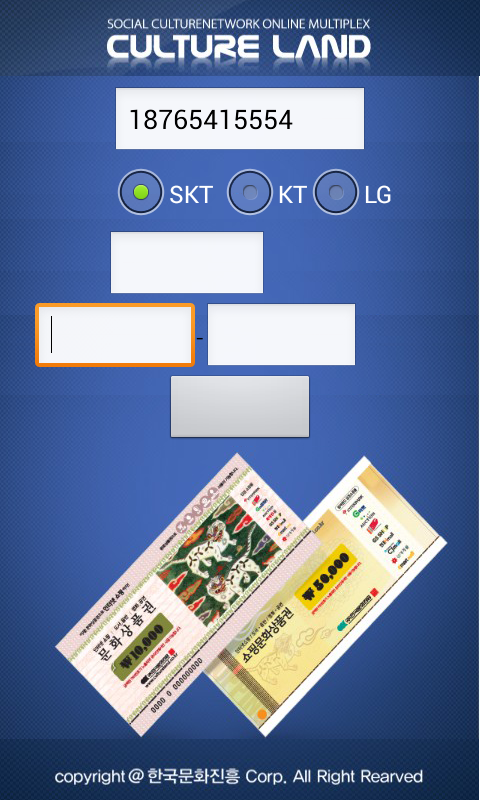
Fig2 : Application Main Screen
If the user clicks on the button shown, a POST request is sent to
hxxp://[REMOVED]2580.com/send_jumin.phpwith parameters
- "sim_no" : [VICTIM's PHONE NUMBER]
- "tel" : [TYPE:{SKT, KT or LG} as chosen by the user (ref Fig2)]
- "name" : [VALUE ENTERED IN TEXTBOX1(ref Fig2), default value "false"]
- "jumin1" : [VALUE ENTERED IN TEXTBOX2(ref Fig2), default value "false"]
- "jumin2" : [VALUE ENTERED IN TEXTBOX3(ref Fig2), default value "false"]
- "datetime" : [CURRENT DATE AND TIME IN FORMAT "yyyy-MM-dd HH:mm:ss"]
Next, an alarm is set to check for the network state every 5 secs. If the network state is "CONNECTED", the value of a variable cmdString is read and depending upon its value, a corresponding function is performed. It's default value is blank.
| cmdString value | Function performed |
| GET_RECIVE_MESSAGE (misspelt) | Sends a POST request to "hxxp://www.[REMOVED]2580.com/send_recieve_count.asp" with the parameters {"sim_no" : [IMSI], "totalCount" : [NUMBER OF SMS IN INBOX]}
For each SMS in the inbox, a POST request is sent to "hxxp://www.[REMOVED]2580.com/send_message.asp" with the parameters {"sim_no" : [IMSI], "_id" : [SMS_ID], "thread_id" : [THREAD_ID], "address" : [SMS SENDER's PHONE NUMBER], "date" : [SMS RECEIPT DATE IN FORMAT "yyyy-MM-dd HH:mm:ss"], "body" : [SMS MESSAGE BODY], "read" : [STATUS INDICATING WHETHER SMS IS READ OR NOT]} |
| GET_SEND_MESSAGE | Sends a POST request to "hxxp://www.[REMOVED]2580.com/send_recieve_count.asp" with the parameters {"sim_no" : [IMSI], "totalCount" : [NUMBER OF SMS IN SENT FOLDER]}
For each SMS in the inbox, a POST request is sent to "hxxp://www.[REMOVED]2580.com/send_message.asp" with the parameters {"sim_no" : [IMSI], "_id" : [SMS_ID], "thread_id" : [THREAD_ID], "address" : [SMS RECEIVER's PHONE NUMBER], "date" : [SMS SNEDING DATE IN FORMAT "yyyy-MM-dd HH:mm:ss"], "body" : [SMS MESSAGE BODY], "read" : [STATUS INDICATING WHETHER SMS IS READ OR NOT]} |
| MODIFY_MESSAGE/td> | Sends a POST request to "http://www.[REMOVED]2580.com/get_cmd_body.asp" with the parameter {"sim_no" : [IMSI]}.
The malware expects a response in the format [READ] + [DATE_STRING] + [SMS_ID] + # + [MSG_BODY]. It searches the inbox for an SMS matching the SMS_ID received and then updates it's value using the remaining parameters i.e. the SMS content is replaced with MSG_BODY, the date with DATE_STRING and READ determines whether the SMS appears as read or unread. |
| DELETE_MESSAGE | Sends a POST request to "http://www.[REMOVED]2580.com/get_cmd_body.asp" with the parameter {"sim_no" : [IMSI]}.
The response contains an integer that is used to identify a conversation in the SMS inbox that is deleted by the malware |
| SHOW_MESSAGE | Sends a POST request to "http://www.[REMOVED]2580.com/get_cmd_body.asp" with the parameter {"sim_no" : [IMSI]}.
The response contains a text string that is displayed on the victim's phone |
Next, a POST request is sent to "hxxp://www.[REMOVED]2580.com/send_finish.asp" with the parameter "sim_no" : [IMSI].
The malware also spies on incoming SMS Messages on the victim's phone with the receiver smsReciever
Whenever an SMS is received, it is forwarded to the attackers in a POST request to
hxxp://[REMOVED]2580.com/send_product.phpwith the parameters
- "sim_no" : [IMSI]
- "tel" : [VICTIM's PHONE NUMBER]
- "thread_id" : [SMS THREAD_ID]
- "address" : [SENDER's PHONE NUMBER]
- "datetime" : [DATE OF RECEIPT OF SMS IN FORMAT "yyyy-MM-dd HH:mm:ss"]
- "bady" (misspelt) : [SMS MESSAGE BODY]
- "read" : 1
- "type" : 1
Finally, the malware is launched automatically each time the phone is switched on and a GET request is sent to
"hxxp://www.[REMOVED]2580.com/post_simno.asp" with "sim_no" = [IMSI]
Permissions required by the application:
- RECEIVE_BOOT_COMPLETED
- INTERNET
- ACCESS_NETWORK_STATE
- READ_SMS
- WRITE_SMS
- WRITE_EXTERNAL_STORAGE
- READ_PHONE_STATE
- WAKE_LOCK
- RECEIVE_SMS
- SEND_SMS
Aimed at Korean users
 Recommended Action
Recommended Action
- FortiGate Systems
- Check the main screen using the web interface for your FortiGate unit to ensure that the latest AV/NIDS database has been downloaded and installed on your system - if required, enable the "Allow Push Update" option.
FortiClient Systems
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiGate | |
|---|---|
| Extended | |
| FortiClient | |
| Extreme | |
| FortiAPS | |
| FortiAPU | |
| FortiMail | |
| Extreme | |
| FortiSandbox | |
| Extreme | |
| FortiWeb | |
| Extreme | |
| Web Application Firewall | |
| Extreme | |
| FortiIsolator | |
| Extreme | |
| FortiDeceptor | |
| Extreme | |
| FortiEDR |
Version Updates
| Date | Version | Detail |
|---|---|---|
| 2019-04-12 | 67.75300 |