Android/FakeNefix.A!tr.pws
 Analysis
Analysis
Android/FakeNefix.A!tr.pws is a malware which targets Android mobile phones.
It is designed to look like the legitimate Netflix application (on-demand Internet streaming media), but is malicious: its splash screen requests user credentials.
Those credentials are sent to a remote malicious website.
After sending the credentials the malware warns the end-user it cannot work
properly (see Figure 3) and uninstalls itself.
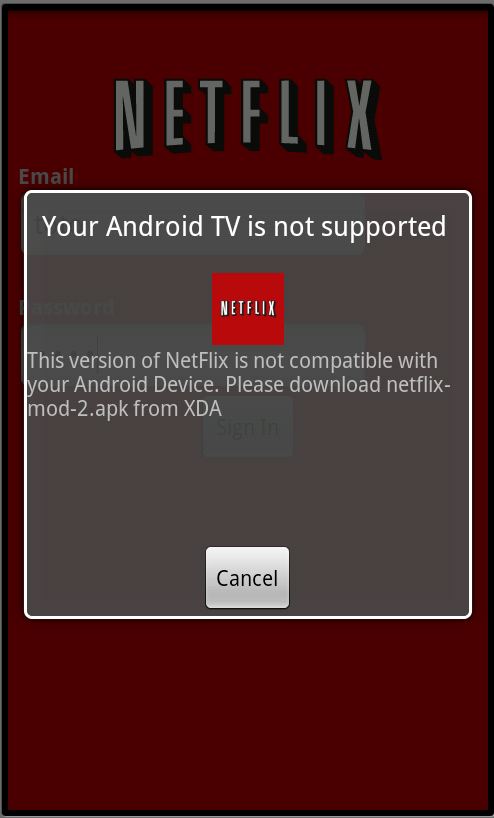
Figure 3. The malware notifies the victim it cannot work properly (fake).
Technical Details
There is barely anything technical about this malware. Its danger relies on social engineering: the application looks like the real Netflix application.
In reality, the malware does absolutely nothing else than display a splash screen that requests login credentials. Once those credentials are entered, they are posted via HTTP to a remote web server:
http://ero[CENSORED]-ip.biz/login.phpwhere information posted is:
- email: login
- pass: password
 Recommended Action
Recommended Action
- FortiGate Systems
- Check the main screen using the web interface for your FortiGate unit to ensure that the latest AV/NIDS database has been downloaded and installed on your system - if required, enable the "Allow Push Update" option.
FortiClient Systems
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiClient | |
|---|---|
| Extreme | |
| FortiMail | |
| Extreme | |
| FortiSandbox | |
| Extreme | |
| FortiWeb | |
| Extreme | |
| Web Application Firewall | |
| Extreme | |
| FortiIsolator | |
| Extreme | |
| FortiDeceptor | |
| Extreme | |
| FortiEDR |